ISACA, an independent, non-profit, global association for IT governance professionals, publish an annual report of the results of their global State of Cybersecurity Survey. The 2018 version of this report shows that “Skills challenges remain, but are better understood. The skills gap continues unabated. Enterprises still have open security positions, and the time to fill them appears to have decreased slightly.”
Unfilled security positions
“Fifty-nine percent of enterprises report that they have open (unfilled) security positions”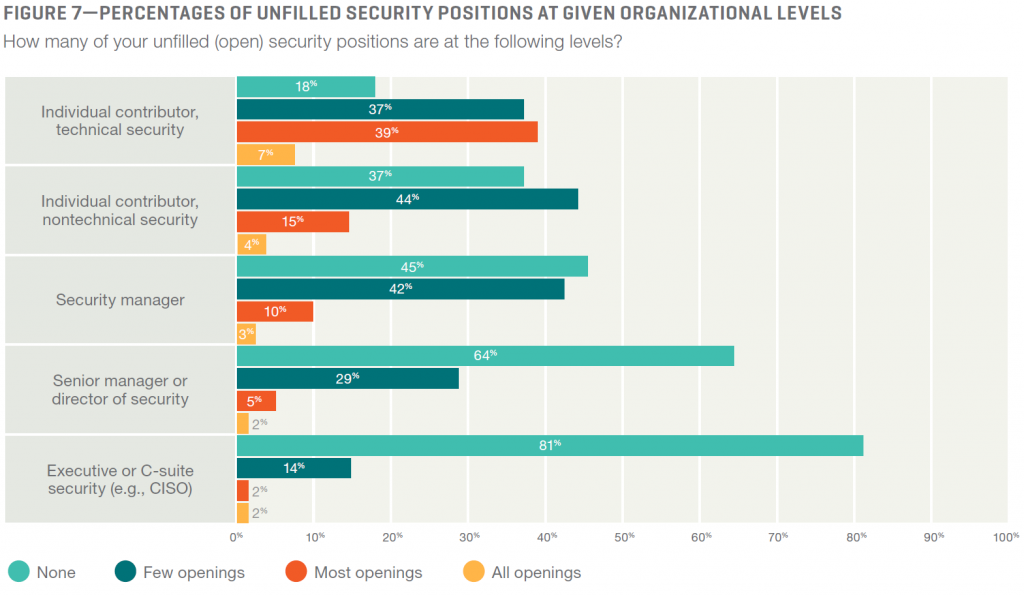 As you can see, there are few gaps at CISO (Chief Information Security Officer) level, so that should mean that policy is created. However, any gaps at Director of Security level may mean there is not enough focus on implementing the policy and ensuring that working practice is in line with the policy. The gaps at the lower levels present risks at the operational level. Policy alone won’t stop there being a security breach and making the press for losing customer data!
As you can see, there are few gaps at CISO (Chief Information Security Officer) level, so that should mean that policy is created. However, any gaps at Director of Security level may mean there is not enough focus on implementing the policy and ensuring that working practice is in line with the policy. The gaps at the lower levels present risks at the operational level. Policy alone won’t stop there being a security breach and making the press for losing customer data!
Likelihood of Cyberattack
 “Eighty percent of respondents indicate that it is either likely (38 percent) or very likely (42 percent) that they will experience a cyberattack in 2018.” Are you confident you have the right people with the right skills and experience, and the appropriate level, to avoid your next attack being catastrophic?
“Eighty percent of respondents indicate that it is either likely (38 percent) or very likely (42 percent) that they will experience a cyberattack in 2018.” Are you confident you have the right people with the right skills and experience, and the appropriate level, to avoid your next attack being catastrophic?
“The potential for an increase in enterprise security budgets will be welcome news for many practitioners. Not only does it bring opportunities to acquire necessary tools, but also boosts resources for talent acquisition, training and skill building.” Has your budget increased? Do you have the funding to keep up, and to ensure that you baseline current skills, so you know which skills need to be acquired, trained or built?
Business disruption
 As Gartner reported in March 2018, “by 2020, 75 percent of organizations will experience visible business disruptions due to I&O [IT Infrastructure & Operations Management] skills gaps“. They went on to suggest that “Given the lack of digital dexterity for hire, I&O leaders must begin by developing these skills with the talent they already have. Most companies don’t have an accurate inventory of the available skills of their current IT workforces, so this must be a first step.”
As Gartner reported in March 2018, “by 2020, 75 percent of organizations will experience visible business disruptions due to I&O [IT Infrastructure & Operations Management] skills gaps“. They went on to suggest that “Given the lack of digital dexterity for hire, I&O leaders must begin by developing these skills with the talent they already have. Most companies don’t have an accurate inventory of the available skills of their current IT workforces, so this must be a first step.”
Whether your approach to skill gaps is to develop your existing workforce or recruit additional staff, or both of these, surely it is essential to start with a clear understanding of the current skills available in your organisation.
Skills Framework for the Information Age (SFIA)
SFIA is the de facto standard for describing Digital, IT and Cybersecurity skills. It is used by governments and companies in nearly 200 countries around the globe. SFIA versions over the last few years have devoted significant attention to ensuring the framework covers all the Information and Cyber Security skills that are needed in the working world. As part of the project to produce SFIA7, released in 2018, discussions were held with a number of global Cybersecurity related professional bodies, large employers and bodies of knowledge. This confirmed SFIA as an ‘umbrella’ framework for detailed descriptions of cybersecurity skills and tasks. SFIA covers everything from Strategy and Architecture, Governance and Policy, through to specialist skills such as Penetration Testing and Digital Forensics, to Design, Operation, Security Administration, Access Control, and Incident Management – and many more.
Specific references to security in SFIA7:
- Generic Levels of Responsibility: Business Skills (all 7 levels) – covering an individual’s generic need to understand and respond to security practice, embedding it within their normal working practice
- Information Security (SCTY)
- Information Assurance (INAS)
- Solutions Architecture (ARCH)
- Data Management (DATM)
- Systems Development Management (DLMG)
- Software Design (SWDN)
- Programming / Software Development (PROG)
- Real-time / Embedded Systems Development (RESD)
- Network Design (NTDS)
- Testing (TEST)
- User Experience Design (HCEV)
- Hardware Design (HWDE)
- Asset Management (ASMG)
- Change Management (CHMG)
- Security Administration (SCAD)
- Penetration Testing (PENT)
- Application Support (ASUP)
- IT Infrastructure (ITOP)
- Database Administration (DBAD)
- Storage Management (STMG)
- Quality Management (QUMG)
- Conformance Review (CORE)
- Digital Forensics (DGFS)
- Sourcing (SORC)
- Supplier Management (SUPP)
In addition, there are other skills which are relevant and often included in the Job Descriptions for Information and Cyber Security professionals which don’t mention the word ‘security’ specifically, as it is just one of the areas that might be covered by the skill. These include Enterprise IT Governance (GOVN), Strategic Planning (ITSP), Information Governance (IRMG), Analytics (INAN), Consultancy (CNSL), Specialist Advice (TECH), IT Management (ITMG), Enterprise and Business Architecture (STPL), Business Risk Management (BURM), Systems Design (DESN), and Incident Management (USUP).
Skill gaps
Where are your gaps, and which skills do you need to prioritise for development or recruitment?
A baseline skills assessment will ensure you know where your strengths and weaknesses are, opportunities to exploit skills that are not currently being utilised, as well as confirm risks or threats. With an appropriate approach, backed up by a good toolset like SkillsTX, you can build the accurate inventory of available skills that Gartner urges all companies to build as their first step.

